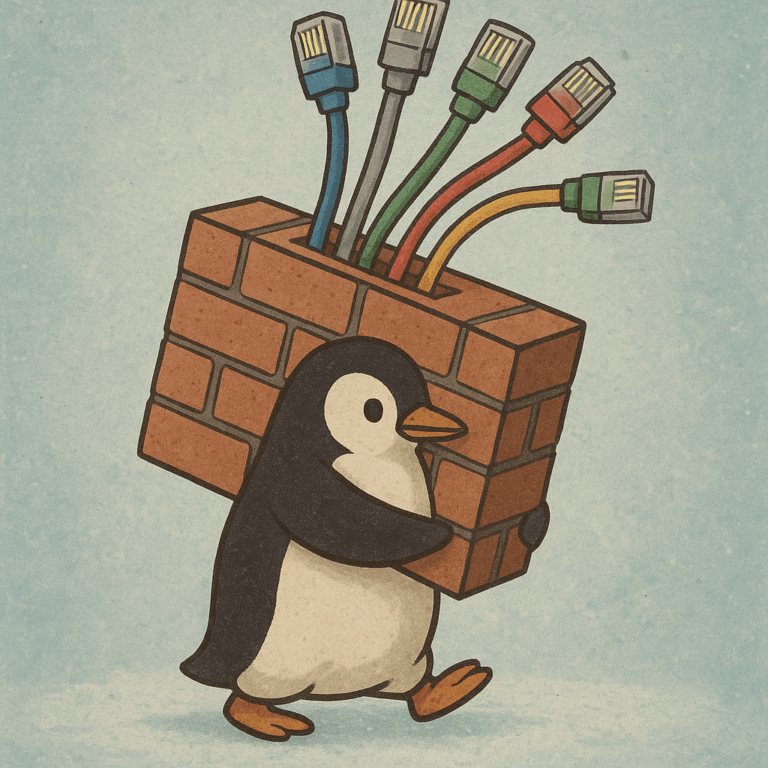
Linux router firewall configuration with NetworkManager and firewalld
Introduction I use Linux as an Internet router. I use it with multiple rules (rather simple) using a very simple baseline configuration. The router has two main network interfaces – one facing the internal LAN, and one facing the external fibre connection, where it needs to use a specific VLAN, and then – use PPPoE…